
Exploiting the Telnet Vulnerability on Metasploit 2
This post continues from my last one, Exploiting Metasploitable 2 Using Nessus and Metasploit Framework. In this one, I’ll use Nmap to gather more information about the machine’s open ports and possible vulnerabilities.
Scanning the Target
Running a port scan on the Metasploitable 2 machine produces the following results:

Focusing on Port 23 (Telnet)
For this post, I’m focusing on port 23 (Telnet). The Nmap scan identifies the service as Linux telnetd. When running a search for Telnet-related exploits using searchsploit, no useful results are found in this case:

Connecting via Telnet
Since Telnet requires a username and password to log in, we can try connecting to the port manually using:
telnet <ip address>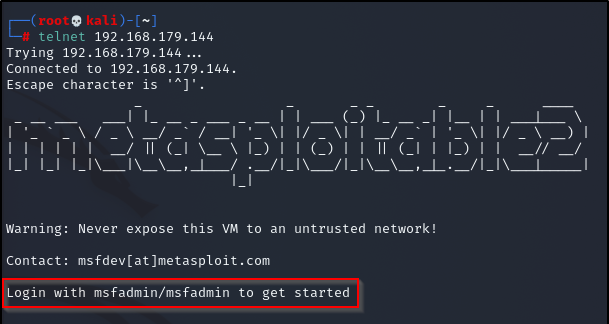
In the screenshot above, you’ll notice that login credentials are displayed – which, of course, should not happen. This is a classic example of information disclosure.
Using the displayed credentials, logging in as the user msfadmin is successful. Since we have the password, we can easily escalate our privileges to the root user:
sudo su
Metasploitable 2 is designed as a vulnerable test machine, and while it’s relatively easy to gain access to, it feels great making steady progress while practicing these techniques every day.


